WEEK ONE
Session 1
In this class session we went over the class structure and the syllabus. We discussed chapter 1 on the importance of MIS. This is a short summer session packed with 12 chapters of material, so following the syllabus and staying up on reading is important.
Managing information systems is important to study going into the digital future. As development of newer and higher functioning computer systems creates more efficiency, human beings will have to acquire different skills and greater skill in particular areas, to move into the new market on jobs. The most highly valued skills will pertain to managing information systems. The purpose of this class is to focus on these new skill sets that will differentiate the successful student as someone capable of using critical thinking and problem solve skills with the systems being developed. Human beings will still need to fulfill the creative thinking and collaboration areas that AI cannot perform.
Session 2
The five component framework consists of: Hardware, Software, Data, Procedures, and People. In setting up and valuing an IS you need to consider how much data you are handling to determine what hardware and software you need. The scope of the project becomes important. The type of setup you use will be determined by how much and what type of data use is involved. The process and people will be determined and valued based on this intended use for functionality. In finishing up chapter 1 it is important to remember that information is an input output relationship and that data does not become information until it is interpreted. Data can be interpreted in a variety of ways and it is important to keep in mind both ethics and scale with the context of the data. Data has some important properties: Accuracy, Relevance, Timely, Sufficient, Worth it’s cost. These are the aims we try to meet with sourcing data.
In wrapping up, there is a lot of growth and human potential to be put to use as we appreciate the efficiency gains in growth from Bells law (a new computer class every decade), Moore’s law (transistor squares per square inch doubles every 10 mos), Nielsen’s law (network connections increase by 50% per year). In doing so we will need to excell in the non-routine skills: abstract reasoning, system thinking, and collaboration.
Session 3
Wrapping up week one we discussed the individual project on the Tableau website in which we will analyze and visualize data in a short project with paper. This encompasses the ideas from the first chapter and the five components of a network. With regard to data, I asked the question as to whether Tableau data site is similar to Google Mapping for data mapping. The answer to this is that Tableau is not only a data set access point, but also has software built in for managing and analyzing the data, therefore it also aids in the people and process portion of the five components.
chapter 2 discusses competitive strategy and the five forces model.
The Five Forces are:
- Bargaining Power of Customers
- Threat of Substitutions
- Bargaining Power of Suppliers
- Threats of New Entrants
- Rivalry
The Four Strategies are:
- Cost Focus
- Differentiation Focus
- Industry Wide
- Segment Only
The competitive forces can be thought of on a scale from weak threat/force to strong threat/force and can function on an acid with strategy type to get mixed responses to different industry types and approach can be relatively elastic.
WEEK TWO
Session 4
Going into week two we continue the conversation about the five forces and competitive strategy. We watch the porter video on how competitive behavior in the value chain may not be the best strategy with suppliers and distributors. One of the best ways to create value and be competitive in the market with rivals, producing similar goods, is to form alliances. When supplier and demander don’t compete with one another for their share of the market value, together they can out-compete others. As porter notes it is a move to creat “integrated cross departmental business systems”. It points to maximization of the business process competitive advantage in which we recall locking in customers/buyers with high switching costs (contractual agreement and mutually shared platforms or services), barriers to entry (difficulty getting into the market where already built systems and alliances exist) cost reduction (alliances create greater mutual cost benefits and hard to break bonds)
GROUP WORK
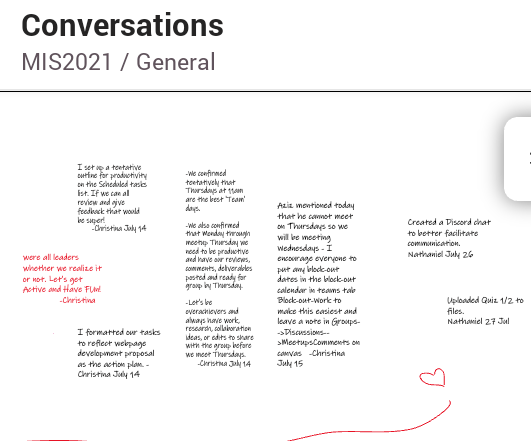
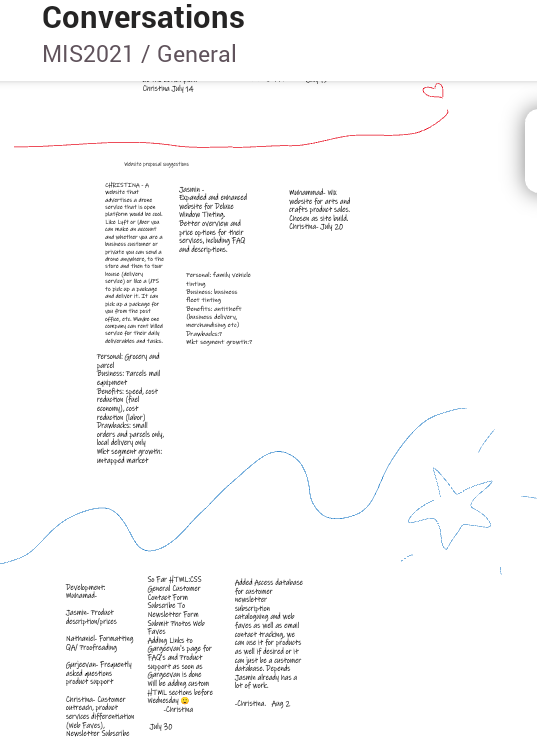
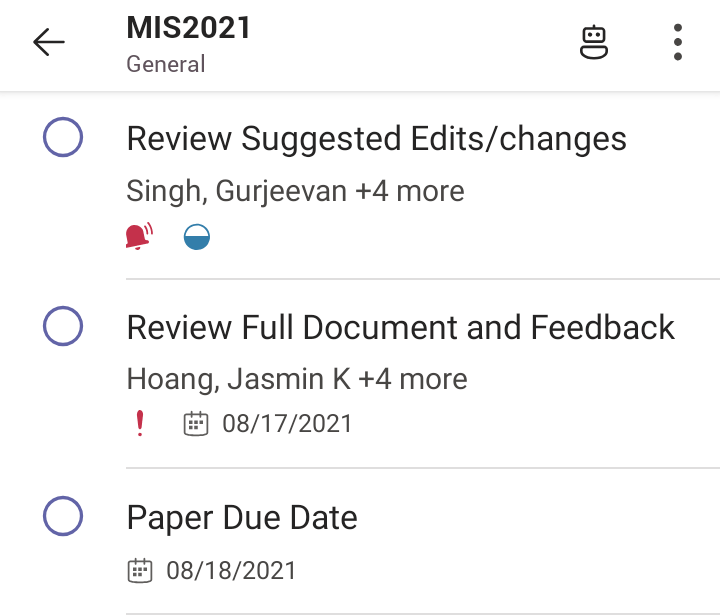
We determined the relative structure of our project last week and I created a Microsoft Teams collaboration group. The rough outline of project objectives and due dates was made along with a files upload tab, a work and schedule needs calendar for individuals, and a conversation Whiteboard for collaboration notes. I added a link to update in canvas all important notifications. While this has never worked before with any of my groups due to human behavior and a tendency to to use chat quickly and start random events in Google docs asynchronously from a larger ‘group collaborative organizational strategy’ like Teams. Immediately following the creation of the integrated group organizational strategy’ someone posted a new team chat channel under teams rather than using the one in the collaboration page. I will keep trying.our general group deadlines are under way though we already had some scheduling conflicts and confusion. Rather than using the whiteboard space to post ideas the team went ahead and made a decision in group face-time. I was amicable to the decision and looking forward to meeting the rest out our deadlines and challenges.
Session 5
In chapter 8 we discuss processes, organizations, and information systems. We discuss efficiency between these workgroups created to facilitate the input output relationship between people, procedures, data, hardware, and software as our workgroups churn inputs into output. We recall that data is not information untill it is interpreted .
Efficiency is created when workgroup ratios of input to output are increased. We use methods that are geared toward the organizational strategy’ and note that some processes are dynamic and others are structured. An ERP system can help create efficiency by integrating applications. A CRM system can create efficiency by integrating our customer database, EAI is a virtually integrated database (metadata) that integrates all of our system databases for optimal efficiency. This effectively creates efficiency integrating our five components. To accomplish this goal, ERP systems have applications that support integration of:
- supply chain
- manufacturing
- CRM
- human resources
- manufacturing
Session 6
We finished up our discussion with a video on total ERP and a discussion about avoiding information silos . Information silos create data integrity problems, as mentioned in chapter 5 in discussions about the importance of proper data handling and tables, primary keys, and relationships . Integrity becomes important when you start integrating each database intra-organizationally. As mentioned in chapter 5, it is difficult to reorganize systems with preexisting data problems. It is much easier to organize the system correctly before implementing a total integration system. The implementation of total ERP and EAI (Enterprise Application Integration) will reduce integrity problems and create efficiency across platforms and departments when integrated and maintained properly.
GROUP AGENDA
WEEK THREE
Session 7
We began week three with a group quiz. We are beginning week three with chapter 6. Cloud computing efficiency gains are maximized by pooled resources , taking advantage of resource elasticity . Pooled resources make use of internet and data easier by allowing users to virtually rent equipment and storage space. Start-up costs are lower, maintenance can be cheaper and outsourced, and efficiency can be created across markets like a time share. You only use what you need and that makes costs cheaper.
Session 8
Continuing our discussion of cloud based services and outsourcing hardware, software, and Internet needs, we discuss Pass, Iaas, Saas, and business needs.
- Pass
-
Allows the organization to use a designed platform as a service
-
The vendor provides the hosted computers as a service (VM- Virtual Machines)
Windows Azure with built in Windows and SQL is an example
- Iaas
-
Infrastructure as a Service uses a bare data storage server package to act as a virtual network but does not include other hardware services like SQL
-
rackspace.com isa example of Iaas
- Saas
-
Offers software as a service and the system is fully maintained by the lessee for ease of use for the leaser of the service
-
An example is Microsoft Office Suites, which provides data cloud storage, office word processing software, data processing software, database management software, browser and internet software, and many options for virtual desktops in addition to a host of other services.
Session 9
We discuss advantages and disadvantages of the cloud as a shared platform and or service. Many organizations have very specific security needs that make their online presence a concern. Often companies use a virtual private network , using a tunnel or virtual private path to connect remotely to their internal Network. This method uses public internet and encryption to enhance safety. Companies may use a private cloud that is owned and operated by the organization to enhance security and more safely operate their VPN.
Often companies use a virtual private cloud to reduce internal storage needs so that they limit what is stored locally and store less sensitive information on the VPC. Some information is restricted for certain users or all users outside of the network for security, therefore you may only have access to some information when on the private network and more specifically within the company building.
Companies use various different types of networks to move information including Local Area Network, Wide Area Networks, and Content Delivery Networks . WAN span outside of one geographical area whereas LAN are a local network within close proximity, like in your accounting building and your human resources building in the space next over in the company property. Decisions about security and your network are important because whether you use WAN or LAN, your data are transmitted using the intranet or the internet but they are still transmitted on the net.
CDN’s or content delivery networks store and l deliver content as a platform service, using hardware and software that may be leased by your company, but it may be less secure than your own mainframe or internal data system. Companies that handle sensitive account and financial information, in example, may require secure internal networks to process and store account information. Your accounting department may want to use the private personal database and a LAN with the intranet being local and restricted.
GROUP PROCESS
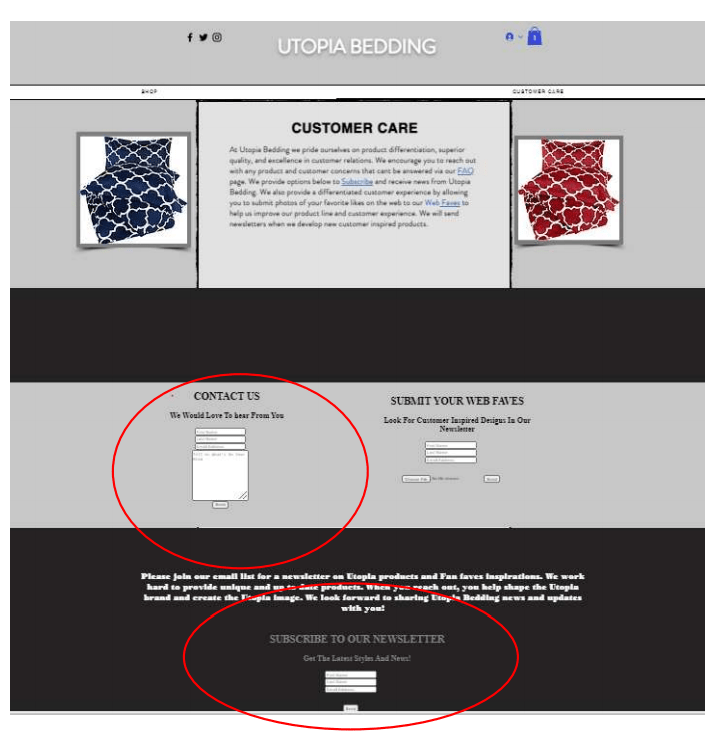
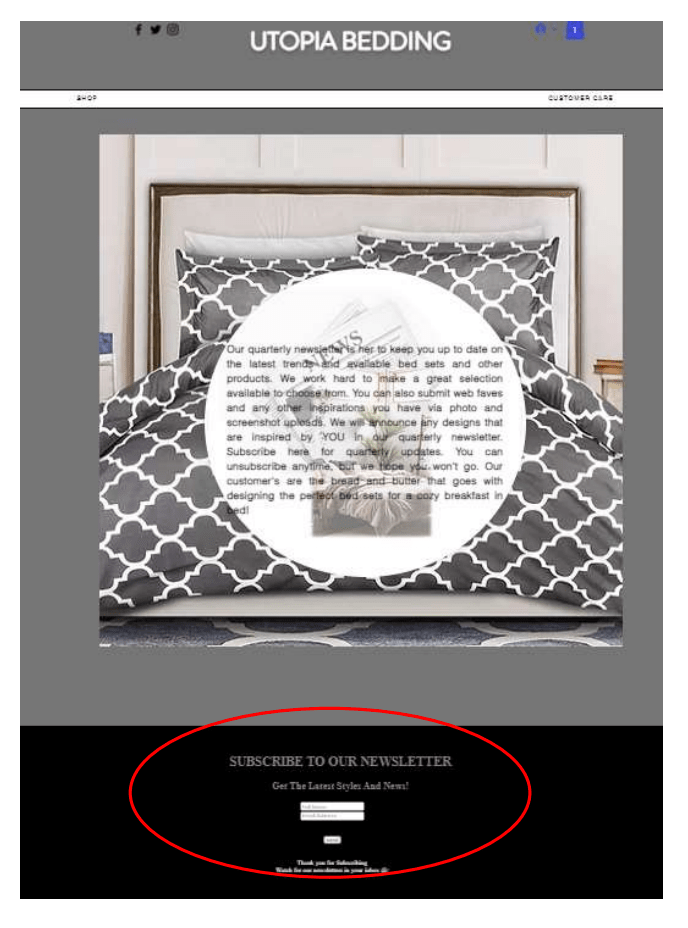
CUSTOMER CARE
I chose customer care for the web build so I will be using my knowledge in MIS and html to build the customer care feedback loop and CRM basics in Access.

WEEK 4
Session 10
This week we are going over chapter 5 databases and intelligence SQL etc. There is unlimited metadata in the world relating to every view, query, submission, and business transaction on the internet. All of this data is collected, stored and used in various ways. To efficiently is data it has to be stored properly and it has to be interpreted properly.
-
DBMS
- Database Management Systems create, process, and administer a database
- The database itself exists in code form
- The DBMS is an application that allows the data to be worked and managed
- IBM and DBZ , Microsoft and Access or SQL , open source often use My SQL
-
Databases
- collection of tables, rows, and columns stored in bytes
- software makes database viewable via DBMS
- primary keys, foreign keys, relationships, entities, and fields give information about the data.
- the data are arranged into schemas and sometimes arrays of data strings
- field properties in DBMS viewer give information such as format, default values, validation, and text rules, required values, indexing, and alignment
- Administering Databases
- administration of the database includes security and access permissions, backup of database, and cleanup and removal of outdated bytes
- development of the database includes creating and staffing DBA functions, form steering committee, specifying requirements, validating data models, and evaluating application designs
- operations include managing processing rights and responsibilities, managing security, tracking problems/managing solutions, monitoring database performance, and managing DBMS
- backup and recovery includes monitoring backup procedures, conducting training, and managing recovery
- adaptation includes setup of requests and tracking systems, and managing configuration changes
- Collections In The Database Application
- forms
- queries
- reports
- they are displayed as visuals in languages like html, c++, and JavaScript called thin client and run in browsers
- Thick Client Languages
- are installed on the computer and run in databases
- thick client languages include visual basic, C++, COBOL, and JavaScript
- Entities, Attributes, and Relationships
- entities are data that needs tracked
- attributes describe entities
- an entity relationship data model is a tool for constructing data models, it describes content, defines entities, and defines relationships among entities
- Data Model Relationship Building
- includes defining minimum and maximum cardinality
- many to many
- one to many
- minimum denoted by cross bars on relationship strings and maximum denoted by cross feet
- no requirement is denoted by an open circle on the relationship strings
- Normalization and Data Integrity
- we want a clearly defined, normalized system of storing and maintaining data
- data integrity means your data is reliable across tables and departments databases
- tables should be clear And have a strong theme with a clear primary key
- one table should connect to another by the same primary key when tracking two different attributes to an entity or by a foreign key when tracking information about an attribute to an entity in which two tables are separate.
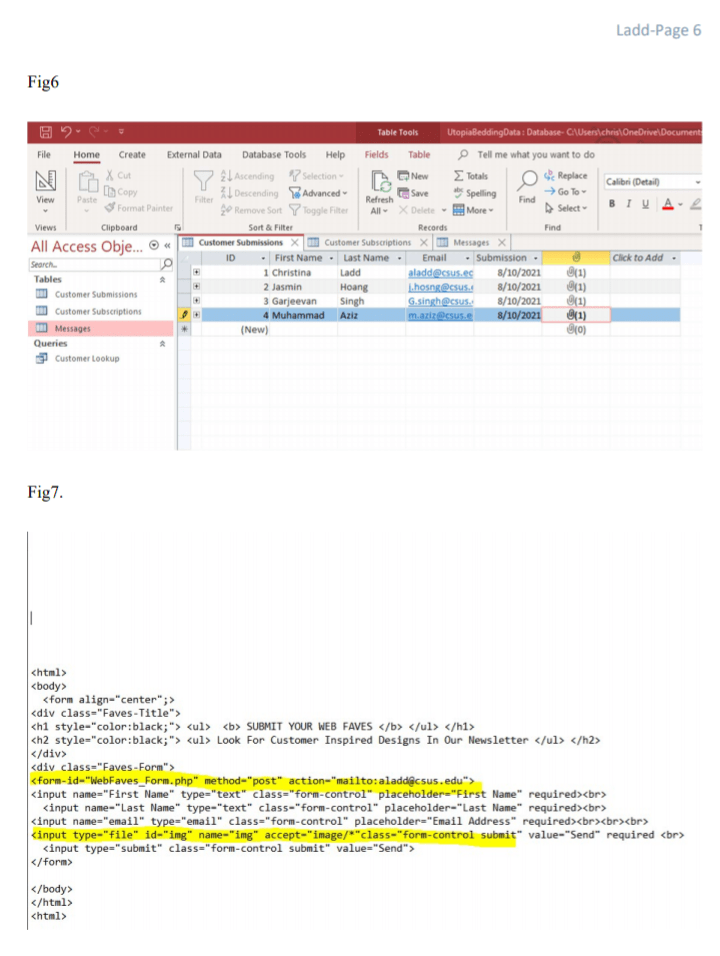
MY COMPLETED WORK DATABASE STRUCTURE AND FEEDBACK LOOP FOR WEB BUILD

WEEK FIVE
Session Twelve
This week we are discussing business intelligence. Businesses use data for intelligence. Data can be sourced personally from the company’s contact and interactions with customers or it can be sourced from data warehouses and data marts. Access to data gives businesses information about purchasing patterns, customer viewing patterns, and leads to predictive data analysis. Data only becomes information once it has been analyzed.
- Internal Data
- pulled from database by running a query
- Analyzed using data software
- information distributed using reports
- reports can be push or pull
- pull are manually requested at the time of query
- push are requested on a regular time interval by you or your organization and are pushed to the user, they may also be pushed on an as needed basis from your organization
- Data Marts and Data Warehouses
- Data warehouses are large DBMS’s that store all types of data
- Data Marts are specialized types of data:
- Web Sales Data Mart
web page design decisions
Store Sales Data Mart
Market basket analysis for sales training
Inventory Data Mart
Inventory layout for item pick
- Data Cleaning
- data needs extracted from:
- organizational databases
other internal databases
external databases
- After data extracting, cleaning, and preparation, data is sent to data warehouse DBMS
- before data cleaning and preparation data often has erroneous email addresses, non-valid or blank fields, misspelling, etc
- after cleaning and preparation data is ready to be pulled or pushed from data warehouses and Marts to users who analyze the data using software for:
-
Sorting
Filtering
Grouping
Calculating
Formating
- RFM
recency
frequency
money
Are measures of analysis
OLAP
Online Application Processing Reports are multi-dimensional
Drill down reports delve deeper into area of OLAP
Multilayer drill down allows user to determine granularity (level of detail) for report
- Supervised
apriori, often with regression equation, contains starting hypothesis
Unsupervised
no hypotheses or models, observance of data only, such as cluster analysis
Session Thirteen
-
Internet security is important because, as discussed in chapter 3, all data and information sent internal and external is sent over the net.
-
Scams and Threats Include:
Phishing
Pretexting
Spoofing
-
ip spoofing
Email spoofing
- wardrivers
-
Incorrect data mod
Systems working incorrectly
Procedural mistakes
Programming errors
IT install errors
Usurption
Unintended service denial
Attacked service denial
-
Antivirus software
Deleting cookies
Trade-off between risk and cost
-
-Company-wide Policy-
What sensitive data is stored
How is data processed
What data is shared interorganizationally
Policy on disclosure to individuals of data stored about them
-The Five Components and Security-
Hardware and Software Technical Safeguards
identification and authorization
encryption
firewall
malware detection
Data Safeguards
data rights and resp
passwords
encryption
system backup
physical security
Procedures People and Human Safeguards
hiring
training
education
procedure design
assessment
compliance
accountability
-
Perimeter firewall protects from external internet transmissions
Local firewall protects LAN internally behind email server level of network
Session Fourteen
Today we discussed SCRUM.
SCRUM is a special time and efficiency technique to team building for project builds.
SCRUM COMPONENTS
Project owner
Scrum Master
Scrum Team
SCRUM PROCESS
Project owner gives details of desired build, deadline, and budget
SCRUM Master works with team talents and roles are assigned
SCRUM Team holds SCRUM meets to determine scope, budget, time and build probabilities
SCRUM Master reviews project projections and approves with Project Owner
When Project owner approves suggested build sprints begin
SPRINT team focuses on one aspect of the build, one Sprint is completed to ensure quality and approved, or sent back to rework
When a SPRINT is complete another can begin, projects are not completed through and sent back repeatedly for each team to fix when errors are detected, but rather completed and checked in SPRINTS for efficiency
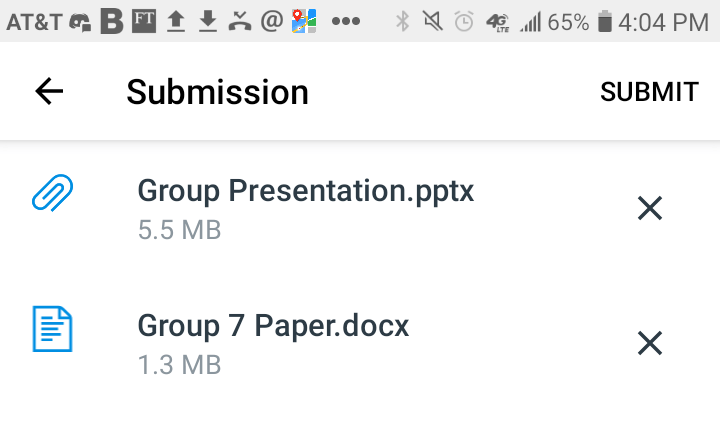
GROUP PRESENTATION
We had a few bumps but our presentation seems to have pulled together nicely. We are formatting our paper. I helped our appointed previewer with some font, title page, and header issues, as his job was last and gave him such a small time budget. Our website is impressive and everyone worked hard. We gave our presentation and are ready for upload. What a long and impacted six weeks. I was so glad to have the opportunity to work on my html with the webb and my journal project.

Personal Project Tableau
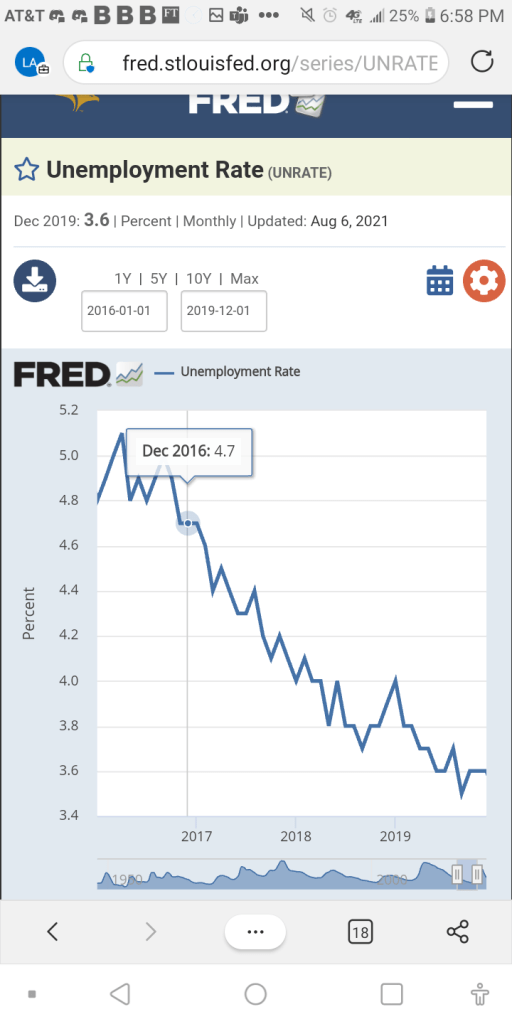
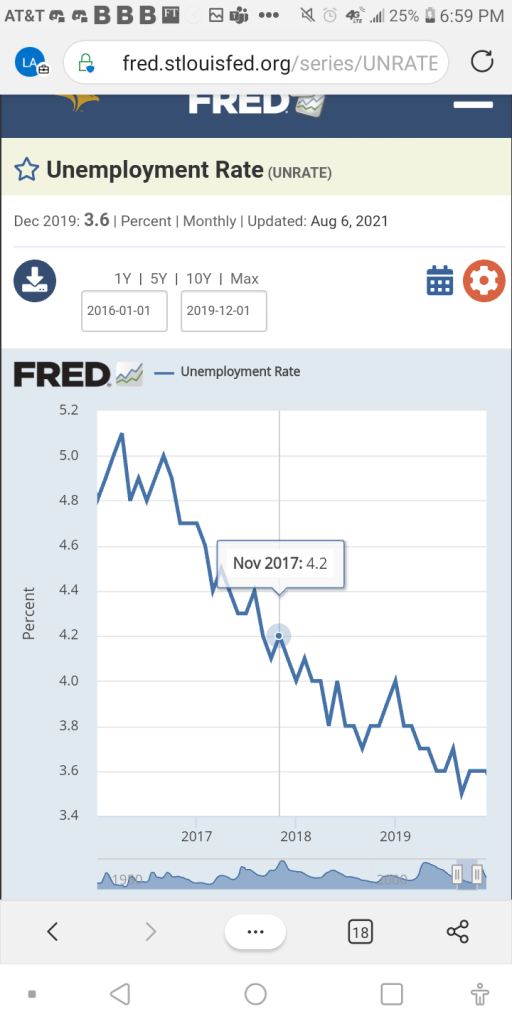
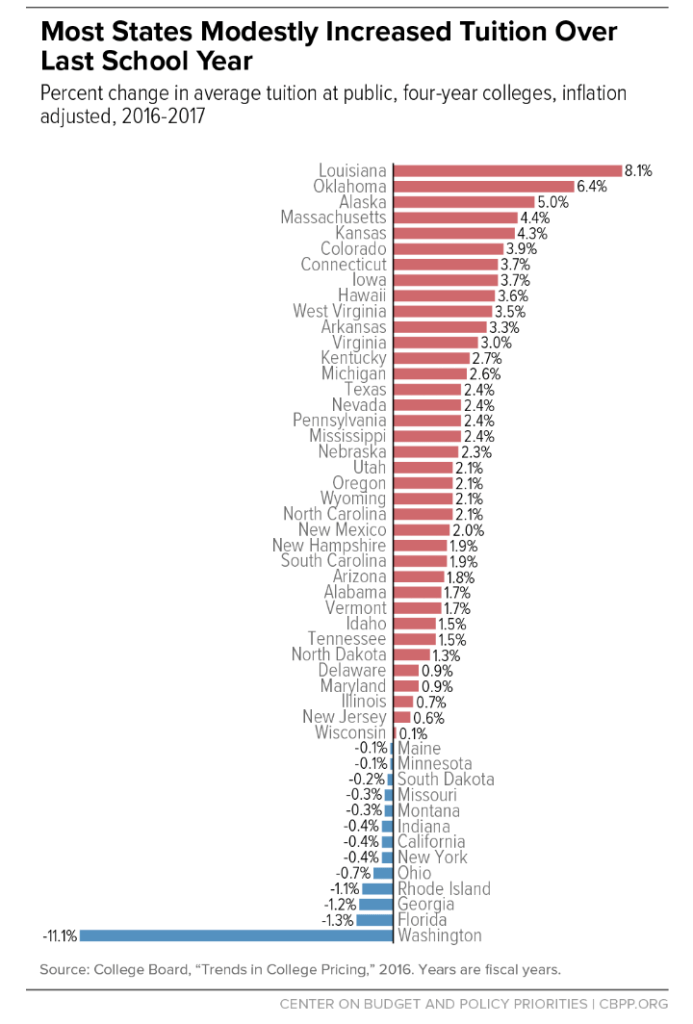
Unemployment and Expenditures on Education
Tableau was challenging with the type of data I am using, but I thought it would be a great opportunity to research inflation, unemployment, and education, as I finish my last couple of courses for my bachelor’s in economics. This was a great class for that because, as we discussed in chapter 1, it is a challenging world out there that is ripe with technological advancements and students will need analytical dynamic and system thinking minds to be competitive in the workforce. This was the focus of my Tableau project. It was challenging, but rewarding to learn a new system in such short time.